Jérôme François
Jeudi 06 juin 2013 à 11h30, salle 55-65/211
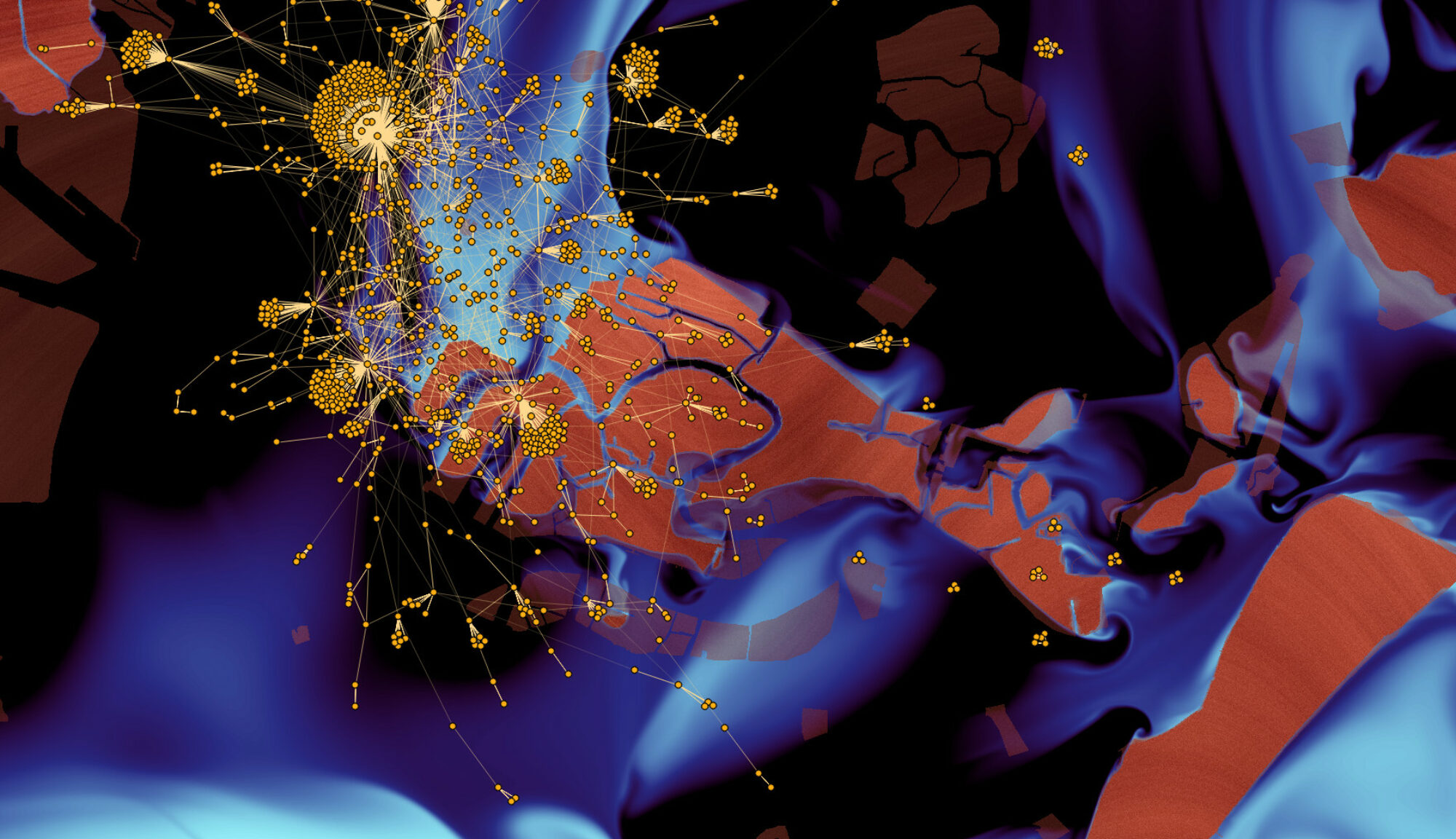
Security issues in Internet force the deployment of defensive measures to protect end users and Internet’s infrastructure itself. While a simple firewall would have been enough in the past, the trend is to promote a deeper analysis nowadays, in particular at the Internet operator level. Simple filtering has to be completed using more in-depth analysis tool. Detection of attacks may have to investigate multiple sources of data meantime and such sources, like network traffic captures, syslog, alerts or locations, may generate huge quantities of data. Forensics alleviates the real-time constraint but requires a perfect and global understanding of an intrusion to recover, protect in future and trigger legal actions as well. Hence, the problem is similar and finding evidences is like looking for a needle in a haystack. Therefore, the seminar will introduce several techniques to cope with big data issues in the context of security. Firstly, flow based methods will be presented as, for example, to track community of hosts participating to a botnet. This is possible by analyzing the traffic flow dependency in Internet and host relationships. Cyber-criminal organizations, like the Russian Business Network, are well organized and constructs their own Internet infrastructure and administrative domains which make them quite resistant to standard counter-measures like IP blacklisting. The seminar will then highlight how to reveal the underlying organization structure at a the Internet administrative domain level.